Staff at MacEwan University, a school in Edmonton, Canada, received an email from a major vendor stating they had recently changed their electronic banking information and needed payments to be sent to a new account.
Assuming their trusted business partner was just going through some changes, the university complied and transferred three payments to the new bank account within a span of 10 days.
But four days later, MacEwan University received a phone call from this same vendor asking them why they hadn't paid their fees yet. Perplexed by the call, the university told them they had just transferred the payments to their new bank account.
The vendor had no idea what they were talking about.
Unfortunately, this bank account didn’t actually belong to MacEwan’s vendor. It belonged to cyber criminals in Canada and Hong Kong. And MacEwan University had just transferred them $11.8 million.
Eventually, the university discovered the email requesting them to transfer their payments to the new bank account was actually fraudulent and a prevalent form of cyber attack that thousands of businesses fall victim to every year — phishing.
Examples of these credentials include passwords, credit card details, bank login information, and social security numbers.Most cyber criminals deploy phishing attacks through email, like the picture below, but some have also started to exploit social media, messaging apps, and text message to steal people’s personal information.
Phishing instances have rose in number over recent years — in fact, there were over over 60,000 phishing sites reported in March of 2020 alone. This cybercrime could wreak havoc on your brand and bottom line.So how do you defend your customers and employees from phishing without making them your brand’s first line of defense?
Here are three shields you can leverage to protect your brand from these prevalent attacks.
How to Protect Your Business From Phishing Attacks
1. Build a DMARC record.
DMARC (Domain-based Message Authentication Reporting and Conformance) is a cutting-edge email authentication protocol that leverages two other authentication protocols, SPF (Sender Policy Framework), and DKIM (DomainKeys Identified Mail) to verify legitimate messages sent from your domain and block fraudulent emails that appear to be sent from your domain.
These email authentication protocols are rather technical, so in a nutshell, SPF is a record of IP addresses that are authorized to send emails on your behalf that email service providers check against, and DKIM is a verification process that leverages cryptographic authentication.
DMARC is the only technology that can ensure your "header from” address (what your users usually look at first when they see your emails) is trustworthy.
To do this, they’ll only authenticate email messages that pass SPF authentication and SPF alignment or DKIM authentication and alignment. If an email message fails SPF authentication or alignment and DKIM authentication or alignment, it’ll fail DMARC.
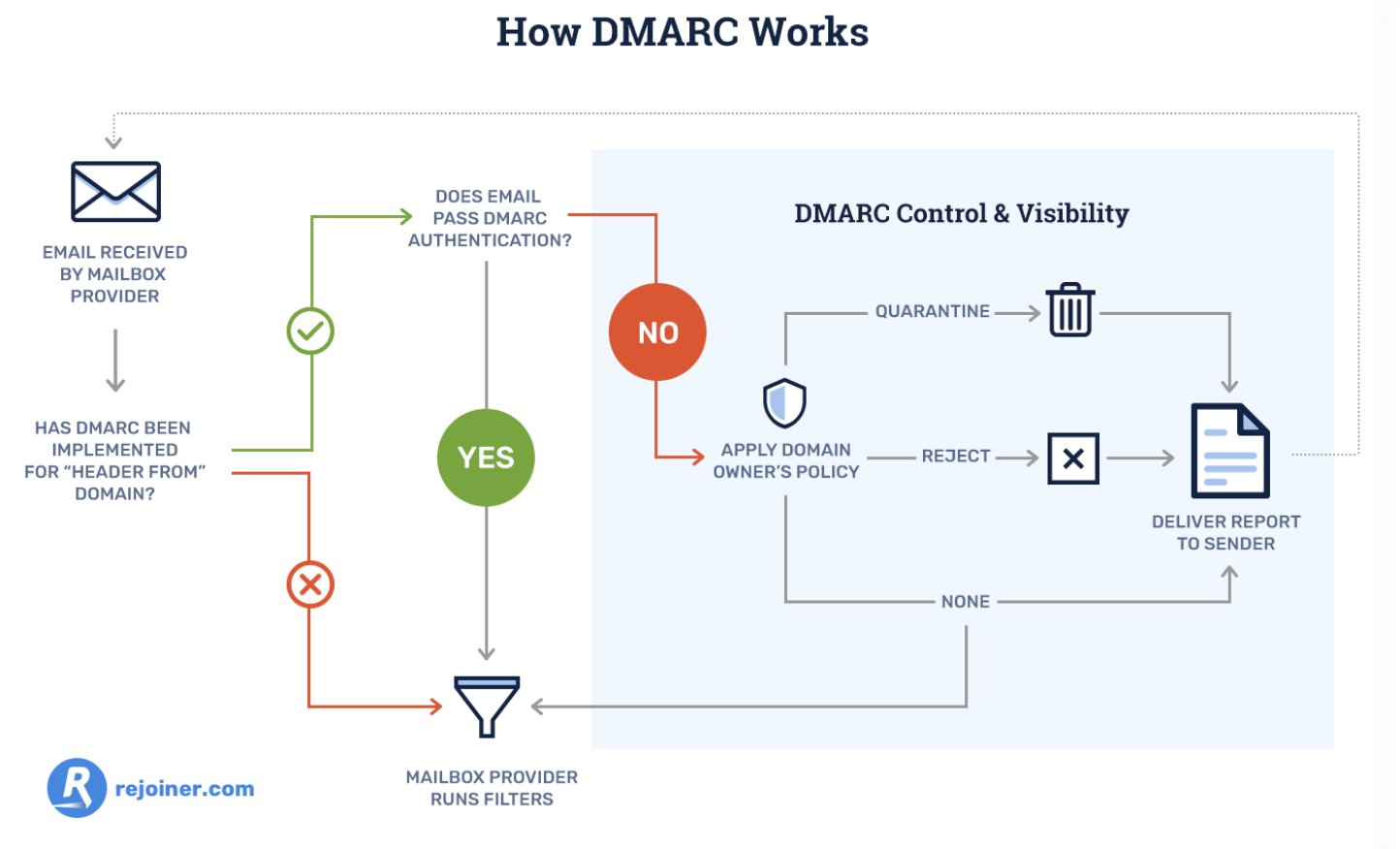
DMARC also allows you to tell email service providers what they should do with any fraudulent mail that appears to be sent from your domain. You can either monitor all of your emails, move unauthenticated messages to users’ spam folders, or decide not to deliver this type of mail at all to inboxes on your server.
Additionally, email service providers will regularly send you forensic DMARC reports, showing you which emails are authenticating, which ones are not, and why.
2. Train customers and employees to spot an attack.
According to PhishMe, a phishing defense solution, companies who train employees to identify and report attempted phishing attacks only have a 5% susceptibility rate to phishing.
To help employees and customers spot one of these attacks and better defend your business, teach them these common phishing markers:
Poor Spelling, Grammar, or Writing
A lot of amateur cyber criminals don’t take the time to craft clear and convincing emails, which brands always seem to do, and foreign cyber criminals will usually rely on Google Translate to translate their messages. So if you receive a poorly written email from a seemingly legitimate sender, take caution.
Suspicious URLs
Most phishing emails lure people into clicking through to a malicious or fake website. To do this, cyber criminals will usually spoof the website’s URL by creating a lookalike one, or they’ll mask their dodgy URL by shortening it.
Whenever you see a weird or shortened URL, make sure you hover your mouse over it to see if the landing page’s web address is different or fake.
Mismatched Sender Address
Even if a cyber criminal can perfectly imitate your brand’s voice, formatting, logo, address, and contact email address in their phishing email, there’s still a trait of yours they can’t copy — your sender address.
Cyber criminals will usually create a lookalike sender address or just use a string of characters in hopes that you won’t check it. To verify a brand’s sender address, check out the sender’s domain in the email’s “from” header and see if it matches the brand’s domain.
3. Invest in email security software.
If your company has the funds, email security software like Proofpoint and Barracuda are the most reliable and effective lines of defense against phishing.
Well-versed employees can still fall victim to cleverly-crafted phishing emails and cyber criminals constantly refine their malicious tactics, like sending phishing emails from the legitimate domains of compromised websites.
But since email security software can identify unusual traffic patterns and monitor fishy URLs, it can effectively detect, block, and respond to these sophisticated threats before they reach your customers and employees’ inbox.
Avoid Getting Snagged
Arm yourself with DMARC, thorough employee training, and the best-fit email security software for your specific systems and situation, to shield your customers, employees, and brand from phishing attacks — no matter how enticing the bait is.
Editor's note: This post was originally published in December, 2018 and has been updated for comprehensiveness.
No comments:
Post a Comment